this post was submitted on 16 Mar 2024
111 points (95.9% liked)
F-Droid
8147 readers
22 users here now
F-Droid is an installable catalogue of FOSS (Free and Open Source Software) applications for the Android platform. The client makes it easy to browse, install, and keep track of updates on your device.
Matrix space | forum | IRC
founded 3 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
Those repos are maintained by the developers of the Monero wallet. So, if they were going to do that, they would also be able to push the malware version to the fdroid repo as well, because the signatures would match the developers.
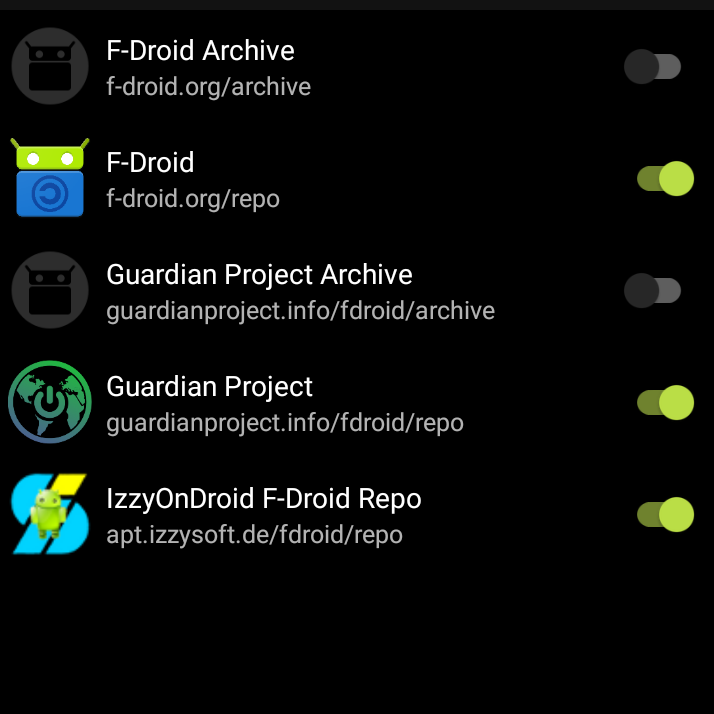
The fdroid repository has only apps built by fdroid itself using the published source code, while a private repo could have a binary that doesn't match the source.
It might be a financial incentive for someone to hack the dev, steal their signing keys, silently add a timebomb that at a specific time would send the whole content of the wallet to a specific monero address, replace the apk after a new release is added. Nobody would notice until too late
Difficult hack but not impossible
That is a fair point. The protection of the main fdroid repo is that they build it from source and then compare the binaries to make sure they match if i understand reproduceable builds correctly.
Edit: But if a hacker hacked the developer, wouldn't they just change the source code as well so that they still match? Like if I wanted to hack Monerujo id want to get the git repo if possible along with the repo keys so i could push malicious code to the git repo, build a binary from that malicious code, publish it on the devs fdroid repo and then when fdroid compares the binary to source they match even though they are malicious.