this post was submitted on 28 Aug 2024
10 points (100.0% liked)
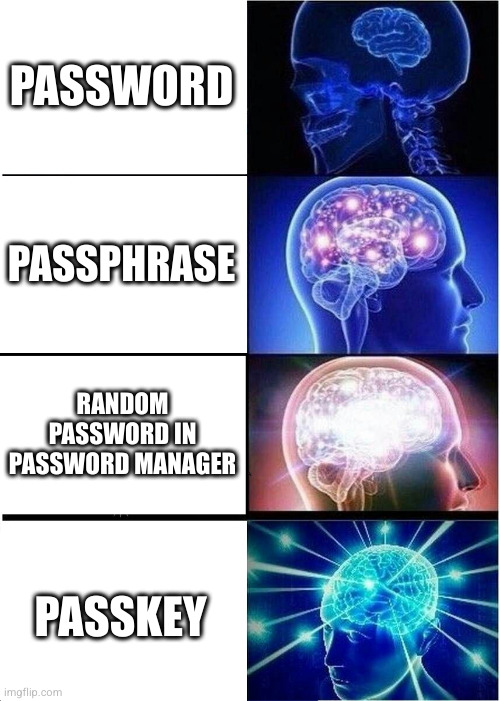
Cybersecurity - Memes
1977 readers
2 users here now
Only the hottest memes in Cybersecurity
founded 1 year ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
I still have no idea how passkeys work. All the explanations I've seen so far were less than helpful.
As I understand it, instead of the website or online service storing your password (in a, supposedly secured way), with passkey your password manager stores a private key and the online service stores a public key (or rather a lock). The key and the lock are paired together cryptographically (mathematical functions that are non-reversible). Now when you login with passkey, the service sends a challenge generated from the lock, that can be solved only with the matching private key, your password manager solves the challenge and your authenticated. Locks and keys were not exchanged during the process, and services never store your key. Everything happens automagically.
It actually uses the same protocol used is some hardware security keys such as Yubikey and Solokeys. The problem remains the same as with hardware security keys, adoption and support, compatibility. It's very rare that a service supports these options, although they exist for a while.
Anyone feels free to correct me if I wrote something wrong. I am by no mean an expert.
Your explanation is correct.
For me, the critical issue is still compatibility. Not all password managers support passkeys, not many sites support passkeys etc.
Imagine SSH Key but for Website
The (over?) simplified version is they’re basically the same as the key/certificate pairs you use to connect to a website securely while also proving its identity to you.
Some key benefits of passkeys are: